Overview
Benthic Software Goldview provides a focused solution for managing remote sessions, credentials, and privileged access in mid to large scale IT environments. Designed to simplify session control and centralize credential handling, this tool streamlines common administrative tasks while improving auditability and security posture. The following article outlines what the solution is, how it operates, its core capabilities, the benefits organizations gain, typical scenarios where it excels, and final guidance for adoption.
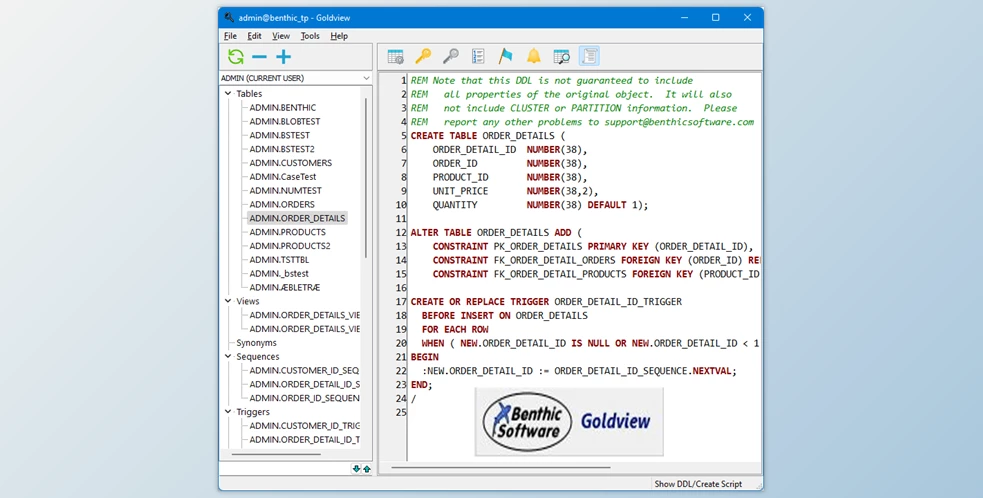
About the product
Benthic Software Goldview is a desktop and server oriented application built to help IT teams control remote access and maintain a secure inventory of access credentials. The product aims to reduce the risk of exposed passwords and unmanaged sessions by providing an auditable chain of custody for privileged operations. It integrates with common infrastructure components to provide a single pane of glass for session monitoring and credential issuance.
Operational overview
The solution works by intercepting or brokering remote connections through a managed gateway, enforcing policies that determine who can connect, when, and under what conditions. Administrators can enforce multi-factor authentication, check out credentials for a limited time, and log session activity for later review. Connections are recorded and metadata is stored to support compliance, forensic analysis, and performance tuning. Integration options allow the product to be incorporated into existing identity and access management workflows.
Primary capabilities
- Centralized credential vaulting with role based access controls to limit who can retrieve or use secrets.
- Session brokering and recording to capture remote activity for auditing and training purposes.
- Automated credential rotation and temporary checkouts to reduce exposure of long lived credentials.
- Policy engine to enforce access rules, session time limits, and approval workflows before access is granted.
- Integration connectors for common directory services, ticketing systems, and remote access protocols to fit into existing environments.
- Detailed logs and activity reports that support compliance efforts and incident response.
- Lightweight client and web interfaces for initiating and supervising sessions from multiple platforms.
- Searchable inventory of endpoints and accounts to make administration and auditing more efficient.
Advantages for organizations
Teams that adopt Benthic Software Goldview can expect to improve operational security and reduce the overhead of managing privileged access. By centralizing credentials and adding session controls, the product helps prevent credential abuse and lateral movement within networks. The audit trails and reporting functions support both internal governance and external compliance requirements. Additionally, automating routine credential tasks frees up administrative time so IT staff can focus on higher value work. The solution’s integrations make it easier to adopt without replacing large portions of existing infrastructure.
Typical use scenarios
- Managed service providers that need to offer controlled access to client environments while maintaining separation and audit logs.
- Enterprise IT operations teams looking to secure privileged accounts across servers, network devices, and cloud services.
- Security operations centers that require recorded sessions and searchable logs for incident investigations and forensics.
- Compliance driven organizations that must demonstrate control over privileged access for audits and regulatory reviews.
- DevOps teams that need temporary access for deployments and troubleshooting, with automatic revocation and rotation of credentials.
- Help desk teams that require supervised access to user endpoints without exposing administrator passwords directly.
- It is the Installer, not the software itself – Smaller, Faster, Convenient
- One-click installer – no manual setup
- The installer downloads the full Benthic Software Goldview.
How to Install
- Download and extract the ZIP file
- Open the extracted folder and run the installation file
- When Windows shows a blue “unrecognized app” window:
- Click More info → Run anyway
- Click Yes on User Account Control prompt
- Wait for automatic setup (~1 minute)
- Click on Start download
- After setup finishes, launch from desktop shortcut
- Enjoy
Conclusion and next steps
Adopting a centralized approach to session and credential management is an effective way to reduce risk and improve operational visibility. Benthic Software Goldview delivers capabilities that address common challenges around privileged access, session monitoring, and credential lifecycle management. Organizations evaluating solutions should map their current access workflows, identify integration touch points such as directory services or ticketing systems, and pilot the product in a controlled environment to validate policies and reporting. With a thoughtful deployment plan and well defined policies, teams can expect measurable improvements in security posture and administrative efficiency.